The Reality Check
Most blockchains operate on a pseudonymous model. Wallet addresses are visible on a public ledger, but they are not immediately tied to a real-world identity. That distinction matters. Pseudonymous systems record every transaction permanently but mask the identity behind it.
Every cryptocurrency transaction is written to the blockchain and cannot be altered. Each transfer creates a permanent record of value movement, time and date, address interaction, and transaction structure.
Every transaction leaves a digital fingerprint. The challenge is not seeing the data. The challenge is interpreting the transaction and details.
At Sphere State, our work focuses on transforming massive blockchain datasets into actionable intelligence that identifies victims, suspects, perpetrators, reconstructs various patterns, and ultimately links digital assets to real-world actors.
Methodology: How We Trace Blockchain Transactions
Blockchain investigations rely on a combination of on and off-chain analytics, clustering algorithms, forensic heuristics and parallel reconstruction. Criminals frequently attempt to obscure the flow of funds through fragmentation, mixing services, bridges, chain hopping, and complex transactional chains. However, these tactics still leave structural signals.
Below are some of the primary methods used in advanced crypto forensic investigations.
Address Clustering and Heuristics
A single actor rarely uses only one address. Instead, they operate several clusters of addresses under their control.
Through forensic heuristics, investigators can attribute multiple addresses to a single controlling entity commonly known as clusters.
Some of these methods include:
-
Common Input Ownership (CIO) heuristic
-
If multiple wallet addresses are used together as inputs in a single transaction, they are likely controlled by the same entity.
-
Change Address Detection
-
In UTXO-based blockchains such as Bitcoin, transactions often generate a change of output, returning funds to the sender, or sending them to a newly generated address.
-
Identifying these change addresses allows investigators to extend the address cluster.
-
Dusting patterns
-
Small amounts of cryptocurrency are sometimes sent to multiple wallets to identify ownership relationships when funds are later consolidated.
Using some of these heuristics, forensic analysts can reconstruct address
clusters or wallets that represent operational infrastructure used by the
entities that are being looked at.
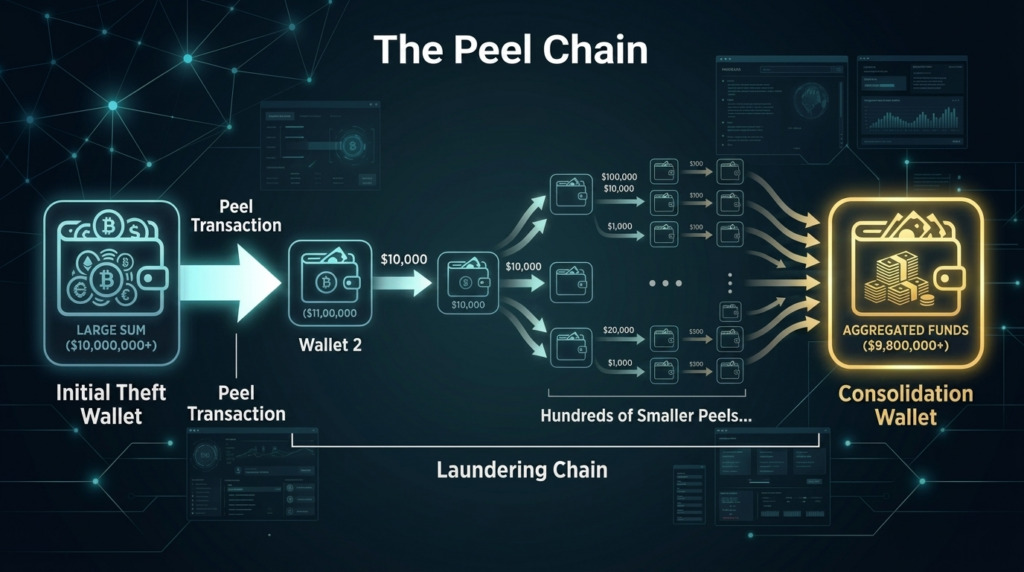
A common laundering tactic is known as a peel chain, not to be confused; this is also a standard typology in Bitcoin spending.
Instead of moving up a large amount of stolen cryptocurrency in a single transaction, criminals repeatedly split funds into smaller amounts across hundreds of transfers.
One typical patter could look like this:
-
A primary address receives stolen funds.
-
A small amount is sent to a secondary address.
-
The remaining balance moves to a new address controlled by the attacker.
-
The process repeats dozens or hundreds of times.
This creates a long chain of incremental transfers designed to overwhelm investigators.
However, advanced blockchain analytics platforms allow investigators to visualize these transaction chains and identify the potential aggregation points where funds consolidate before exiting exchanges or various obfuscation services.
Long peel chains slow investigations but rarely eliminate traceability.
Dealing with Mixers
Most criminals use different mixing services designed to obscure transaction trails.
A well-known example is Tornado Cash, which pools funds pools multiple users before redistributing them to new addresses from various internal funding pools.
Mixers aim to break the deterministic link between sender and receiver. However, they introduce other forensic indicators.
Investigators analyze:
-
Time-correlation analysis
-
Matching deposit timestamps with potential withdrawal windows.
-
Transaction value correlation
-
Comparing unique deposit sizes to possible output patterns.
-
Behavioral clustering
-
Identifying withdrawal addresses that later consolidate funds into known laundering infrastructure.
While mixers significantly increase investigative complexity, they rarely eliminate all observable signals.
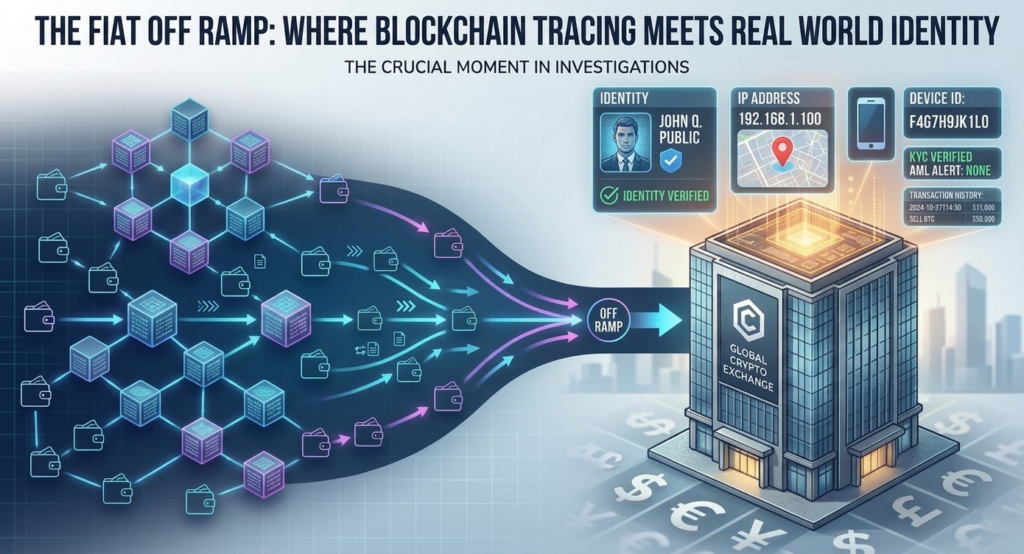
The Bridge to the Real World: Off-Chain Analysis
Blockchain trading is only half of the investigation.
At some point, illicit cryptocurrency typically moves toward a fiat-off ramp where it is converted into traditional currency. These off-ramps often involve centralized exchanges or financial service providers.
This is where attribution becomes possible.
VASP Identification
Investigators trace the transaction path until funds reach a Virtual Asset Service Provider (VASP) such as a centralized exchange.
Examples include:
- Binance
- Coinbase
- Kraken
- OKX
Blockchain intelligence platforms maintain extensive attribution databases that link wallet clusters to known exchanges, OTC brokers, payment processors, and custodial services.
Once funds enter a VASP-controlled address, the blockchain trail intersects with regulated infrastructure.
This moment represents the critical chokepoint in the investigation.
Legal Attribution and KYC Data
Centralized exchanges operating in regulated jurisdictions should maintain Know Your Customer (KYC) records for account holders.
These records may include:
- Verified identity documents
- Registered names and addresses
- Login IP addresses
- Device fingerprints
- Withdrawal banking details
With appropriate legal support, investigators can work with law enforcement or legal counsel to request this information.
This process bridges on-chain attribution with real-world identity, converting blockchain intelligence into actionable evidence for asset recovery and litigation.
Conclusion: Time Is Critical
Digital asset investigations are highly time sensitive.
Stolen funds often move rapidly through multiple addresses, laundering layers, and international exchanges. The earlier an investigation begins, the higher the probability of identifying the laundering pathway and the final custodial endpoint.
Despite the perception that cryptocurrency enables perfect anonymity, blockchain architecture preserves a detailed record of financial activity.
With the right forensic tools, analytical expertise, and legal coordination, those records can reveal the movement of stolen assets and the entities behind them.
If you believe you have been the victim of cryptocurrency fraud, theft, or asset misappropriation, the first step is a structured forensic review.
Sphere State provides free of charge preliminary blockchain tracing assessments to evaluate whether lost digital assets can be followed, attributed, and potentially recovered.
Early action significantly increases the likelihood of success.



